Home » Friend or foe? On the mind-bending potential of quantum computing
Friend or foe? On the mind-bending potential of quantum computing
Quantum computers could solve problems thousands of years faster than today’s machines. They could also crack your password in seconds.
It’s impossible to forget the moment that everything you believe about your profession turns upside down. For Michele Mosca, it happened in the early 1990s when he was studying mathematics and computing at the University of Waterloo. There, the young mathematician first learned of quantum computing — and he didn’t like it one bit.
“I thought it was a joke,” he says of the then-new field. “When I realized people were actually serious about this, I thought it was the craziest thing I’d ever heard of.”
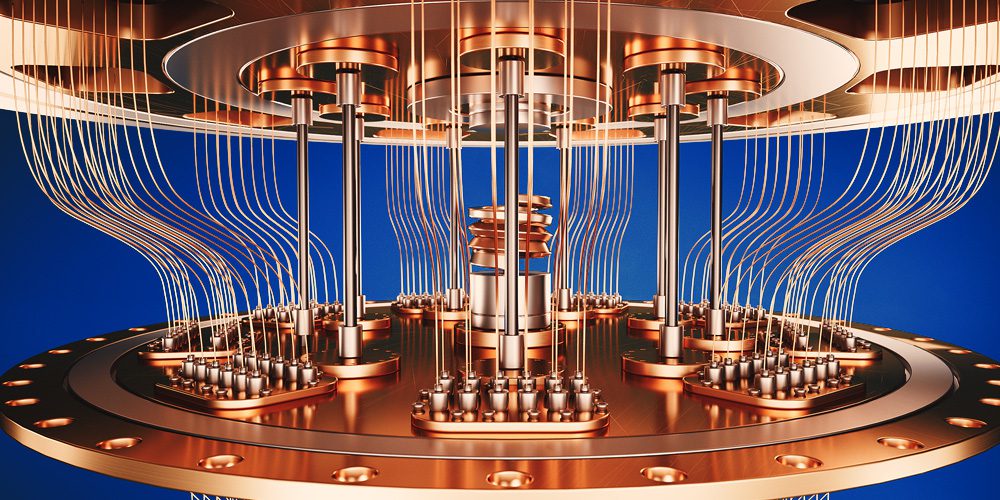
The reason it seemed so outlandish is because it completely rewrote the rule book for what computers could achieve. It did so by taking advantage of the deeply counterintuitive principles of quantum mechanics: a theoretical framework, still only partially understood, describing the very weird behaviour of the smallest constituents of the universe, such as electrons. In theory, quantum computers could solve problems far faster than current computers can — in some cases thousands of years faster.
“Quantum has the potential to open up revolutionary new medicines, or rapidly change how we develop anything from energy storage solutions to carbon sequestration,” says Rafal Janik, head of product at Xanadu, a Toronto-based quantum-computing company. “It might really solve some of the world’s biggest problems.”
But there’s a big catch. Advanced quantum computers will be extremely efficient at solving the kind of cryptographic puzzles that regular computers would take centuries or more to solve. And modern cybersecurity infrastructure is built on that cryptography.
Those long, complex passwords we’ve all been told are essential could be cracked in seconds by a quantum computer. But the potential problems go far beyond the security of your own accounts. On May 4, the White House released a security memorandum stating that quantum computing had the potential to “jeopardize civilian and military communications, undermine supervisory and control systems for critical infrastructure, and defeat security protocols for most internet-based financial transactions.”
Or to be blunt: everything that underpins modern life, from healthcare systems to utility grids to national security infrastructure to banking systems, could be exposed to criminals, terrorists or foreign adversaries.
The consequences could be far more dire than any cyber threat we currently face. “They might not come after you as a personal individual,” says Mosca of hypothetical criminal actors. “They just might come after your economy, your banks, your country. There is material risk to all of us.”
Quantum computing has already been demonstrated by prototype computers working with a few dozen qubits — quantum with training wheels. The real revolution will arrive once these devices achieve quantum supremacy: the ability to perform complex tasks that typical computers cannot.
Today, Mosca is CEO of evolutionQ, a quantum-focused cybersecurity company that works with organizations to prepare for the upcoming quantum shift. He’s also co-founder of the Institute for Quantum Computing at the University of Waterloo.
And he’s changed his tune on quantum since his undergraduate days — its power and possibility are too promising to ignore. But so, he says, is the potential peril: “For the advent of a quantum computer to be a happy day for humanity, we have to first make sure we’ve mitigated the cyber threat that it poses.”
Record now, decrypt later
Quantum mechanics arose in the early 20th century, but it wasn’t until the 1980s that quantum principles started to be applied to computing. To (greatly) simplify, the underlying idea is that a quantum particle can embody multiple positions in space simultaneously. The same goes for a quantum bit, or qubit. Rather than representing a binary, on-off state — the ones and zeros that current computers are limited to — it can embody multiple states, enabling vastly faster computation for certain calculations. Unlike classical computers, which double in power if you double the bits, quantum computers become exponentially more powerful.
So how long do we have before the advent of quantum supremacy and a computer that can easily hack existing cryptography? Hoi-Kwong Lo, a professor at the University of Toronto’s Centre for Quantum Information and Quantum Control, says there is some chance we could see it in as little as five years. But 10 to 20 years is more likely.
“You might say, ‘don’t worry about it now,’ but we are sending our data into the world daily,” he says. “Criminals or others can wait for a few years, hold on to this, and then suddenly access all our secrets.”
Lo is referring to a practice called “record now, decrypt later,” which cybersecurity experts believe criminal organizations and some nations are already engaged in. That, says Lo, “would be a disaster for all of us.”
And the technology is moving fast. In 2019, Google unveiled a processor called Sycamore that it claimed could perform a calculation that would take a supercomputer 10,000 years to do (although these findings were disputed). In 2020, a Burnaby, B.C., company called D-Wave Systems created the world’s first commercially available quantum machine.
Today companies such as Xanadu are also working on different approaches that may advance the technology faster still. Xanadu, which has raised more than $100 million in venture capital and has funding from the U.S. military, is building quantum computers based on photons, individual particles of light.
Because other quantum computers need to be supercooled to about minus 272 degrees Celsius, in order for particles to move through them without resistance, the hope is that photonic computing can provide a more flexible and less costly alternative.
But whatever method of quantum computing breaks through, the technology is coming — it’s just a matter of when.
So, what can organizations do?
The good news is that progress toward quantum-safe (or “post-quantum”) cryptography is also moving fast.
One such technique uses lasers to generate a cryptographic key comprising photons of light transmitted via fiber-optic cables. Due to the complicated properties of quantum mechanics, the data will be useless if intercepted. U of T’s Lo spent several years as a vice president at MagiQ Technologies, one of the few companies in the world making this system commercially available.
But the technology is difficult to scale up for wide application. The real transformation will come with the development of broadly applicable post-quantum cryptography. In 2016, the U.S. National Institute of Standards and Technology embarked on a project that aims to develop, by 2024, new standards for quantum-safe cryptography. European and Canadian regulators are at work on similar projects.
But organizations can’t flip a switch to implement it overnight. Some larger organizations may need years just to migrate their systems — creating an enormous window of opportunity for hackers to strike.
“The first-order problem is just figuring out what cryptography needs to be updated,” says Ehsan Foroughi, chief technology officer with Security Compass, a Toronto cybersecurity outfit.
That can be no small effort.
“One client of ours, a very large organization that runs a huge portion of the world’s computing, has a standard that every software developer they work with needs to follow,” says Foroughi. “It’s 400 pages of controls and standards. And they had a massive problem of updating this enormous document and rolling out the changes across 20,000 engineers. They were reluctant even to touch it, given the effort and cost.”
As chair of the Quantum-Readiness Working Group of the Canadian Forum for Digital Infrastructure Resilience, Mosca has also helped develop guidance and best practices for organizations looking to prepare for the quantum future. Key to those efforts is working with vendors and supply-chain partners to ensure they’re serious about being quantum-ready.
Given the scale of the threat, there’s little that individuals can do to mitigate their own personal risk — an attack on society-scale institutions is an attack on us all. Which is why it’s crucial that those institutions rapidly scale up their response, says Mosca.
“It’s human nature — and the history of cybersecurity shows this — that until a threat is demonstrated, it’s really hard to make people get proactive about it,” he says. “It’s one thing with phishing or ransomware — it’s dangerous, but you can usually do something about it before the floodgates really open.”
With quantum, however, the trickle may become a flood overnight.
“We’re not talking about a small fraction of systems going down or being threatened,” says Mosca. “We’re talking about a big fraction of very important ones, going down in a way that isn’t easily recoverable. The only way to avoid it is to be ready before it’s a problem.”
MaRS believes “innovation” means advancing Canadian technology for the benefit of all people. Join our mission.
MaRS Discovery District
https://www.marsdd.com/
MaRS is the world's largest urban innovation hub in Toronto that supports startups in the health, cleantech, fintech, and enterprise sectors. When MaRS opened in 2005 this concept of urban innovation was an untested theory. Today, it’s reshaping cities around the world. MaRS has been at the forefront of a wave of change that extends from Melbourne to Amsterdam and runs through San Francisco, London, Medellín, Los Angeles, Paris and New York. These global cities are now striving to create what we have in Toronto: a dense innovation district that co-locates universities, startups, corporates and investors. In this increasingly competitive landscape, scale matters more than ever – the best talent is attracted to the brightest innovation hotspots.